While working in any data network, such as a local area network (LAN), the Internet, it is often necessary to restrict access to a particular node to another node of the network, or specific host to all computers under your control. Each computer that uses the data exchange Protocol IPv4 or IPv6, is unique, within certain limits, the number.
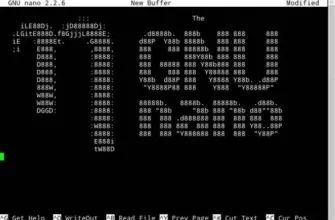
This number is called IP address. We will consider in our article lock IPv4 IP address to restrict access node with the given ID to a particular computer on which we set the rules of the Netfilter firewall with iptables package. In previous articles we have studied the possibility to view the configured rules, to close and open ports. Now for blocking undesirable for us participating in the network exchange information.
How to block ip using iptables
1. How to block a specific IP
To block IP addresses used by the DROP action and REJECT. Describe the General syntax of the action to block.
sudo iptables [-t table] -A [chain] -s [IP address/mask] -d [IP address/mask] -j [action]
Options utility:
- -s [IP address/mask] – IP address of the packet source, to which we want to apply the action;
- -d [IP address/mask] – IP address of the recipient of the package to which we want to apply the effect.
For example, here is a rule to iptables to ban ip blocks all incoming to the protected machine, the packets from the host with IP address 8.8.8.8. It should be noted that the host source of packets when using the DROP action will not receive any feedback from the protected node. For him it will look as if the node is currently not in the network.
sudo iptables-t filter-A INPUT-s 8.8.8.8/32 -j DROP
The second action is to block all packets from a specific node or a specific node is a REJECT. This action provides for the blocking of the package sending the service information to the package source on the blocking performance. That is, in this case, the node of the sender will be notified that the package was blocked by Netfilter. In this case, to block ip iptables it is necessary to perform:
sudo iptables-t filter-A INPUT-s 8.8.8.8/32 -j REJECT

It should be noted that, as in the case of ports, it is possible to block outgoing traffic and incoming traffic. That is, if we want to block access to a specific host on the network to our car, then we block incoming traffic:
sudo iptables-t filter-A INPUT-s 8.8.4.4/32 -j REJECT
If we want to block the access of our computer to a specific node in the network, e.g. the Internet, we block outgoing traffic:
sudo iptables-t filter -A OUTPUT-d 8.8.8.8/32 -j REJECT

2. How to block a subnet iptables?
Blocking specific addresses is a special case of blocking the subnet. A subnet is a strictly limited part of the total IP address space used for addressing a specific subset of all the computers of the global network. Specifies the subnet mask. The mask can be specified in the form of four period-separated numbers or a single number. For example: 255.255.255.0 is the mask visit, and /24 subnet mask. What is the same mask, just written in a different form.
We will not go into the mask value is information for another article. We note only that the set of all IPv4 addresses is broken in the network, networks have classes that define the number of addresses in networks and their practical purpose. And the chains in turn are divided into subnets, private organizations and individuals. And the network and subnet specified by the subnet mask. Now let’s look at how to ban a range of ip addresses iptables.
So, for example, if we want to block access to a specific account, the subset of addresses where we know we will do this by using the known network address (subnet) and the mask. The blocking rule will look as follows:
sudo iptables-t filter-A INPUT-s 8.0.0.0/9 -j DROP
In this case, we blocked the subnet addresses range 8.0.0.0 – 8.127.255.255. Another version of the mask will look like this:
sudo iptables-t filter-A INPUT-s 8.0.0.0/255.128.0.0 -j DROP

To cost to notice that the set of all IPv4 addresses is broken into subsets for individual regions of the world. Therefore, it is possible to block the access of certain regions of the world use to block IP networks. Is results IP networks and logging the issued address blocks from the IANA. For reference, we can track the issued units and block need a separate subnet. For example, this rule denies network issued by the European region:
sudo iptables-t filter-A INPUT-s 2.0.0.0/255.0.0.0 -j DROP

3. How to block IP network interface?
Usually the computer has one physical connection interface. But, there are cases when the protected device has several network interfaces connected to different networks or the same network, but in different ways (protocols, routes, organizations). In this case, it is often necessary to lock the ip iptables with a specific interface. The blocking rule in this case would look like this:
sudo iptables [-t table] -A INPUT-i [interface name input] -s [IP address/mask] -d [IP address/mask] -j [action]
For incoming network interface:
sudo iptables [-t table] -A OUTPUT-o [name of output interface] -s [IP address/mask] -d [IP address/mask] -j [action]
For the outgoing network interface. In the particular case of an incoming and outgoing interface is the same.
For example, to block all packets from IP addresses 8.8.8.8 coming to us from the enp0s3 interface, you can use the rule:
sudo iptables-t filter-A INPUT-i enp0s3 -s 8.8.8.8/32 -j DROP
To block all packets leaving the machine with the IP address 8.8.8.8 from our node through the interface enp0s3 use the rule:
sudo iptables-t filter -A OUTPUT-o enp0s3 -d 8.8.8.8/32 -j DROP

How to find out the available network interfaces and their settings, see configure network from console Ubuntu.
4. How to unblock IP address?
By default, the firewall Netfilters is used the action is ACCEPT for all tables and chains. Therefore, in order to block the IP address, you must add a rule with action DROP, which we considered above. Accordingly, in order to unblock the address, you need to remove already installed a rule. How to remove the already written rule we considered in the article how to remove the iptables rule.
Also in order to restrict access to the computer more strictly, we can replace the default rule ACCEPT rule to DROP or REJECT command
sudo iptables-t [table] -P [chain] [action]
For example, the following command installs the default rule table filter chain INPUT , the default action is to drop packets:
sudo iptables-t filter-P INPUT DROP
In this case, to unblock the IP address iptables, you will need to specify the IP address with the action ACCEPT:
sudo iptables-t filter-A INPUT-i enp0s3 -s 8.8.8.8/32 -j ACCEPT

Insights
So, today we discussed how to block ip iptables, or an entire subnet of addresses. This operation is necessary to deny access to the external host in the network to our computer. We also have in the Arsenal of two actions for such rules – one DROP, will force a remote machine to think that our site currently is absent in the network, and the other, REJECT, allow a remote host to understand that the packet was discarded due to firewall rules.
We also considered the possibility to block packets on a specific interface of a computer that allows you to write very flexible rules, having multiple network interfaces connected to different network segments.